Category

Device storage decides how many applications, photos, and files you can retain on your device....

Malware and ransomware are two types of bad software. They can damage your computer or...

AI is going to change how we work. It can make some tasks easier. But...

Our devices are a big part of our daily lives: work, fun, and staying in...

Ransomware has now become a big problem for many people and businesses. It can lock...

Data breaches can harm your business. They can cost you money and trust. Let’s look...

Malware is bad software that can hurt your computer or phone. It can also make...

File storage and transferring hold a very dear place in most people’s lives. However, the...

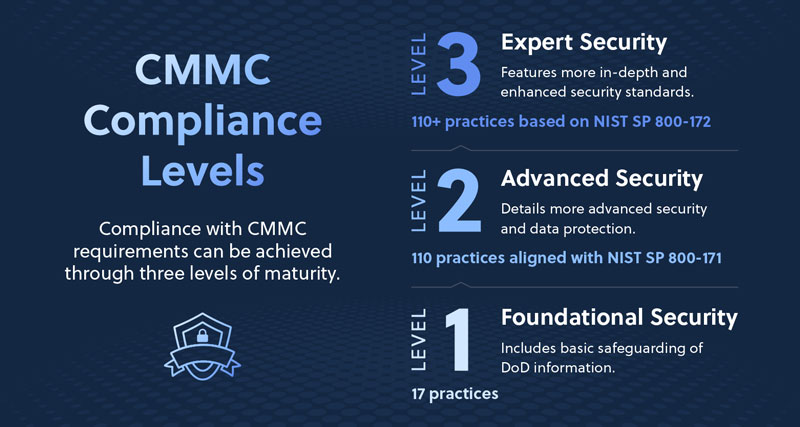
As cybersecurity threats continue to rise and regulatory requirements tighten, organizations supporting government contractors must...
Contact us now to explore customized IT solutions that drive efficiency, security, and success for your business.