Category

Malware is bad software that can hurt your computer or phone. It can also make...
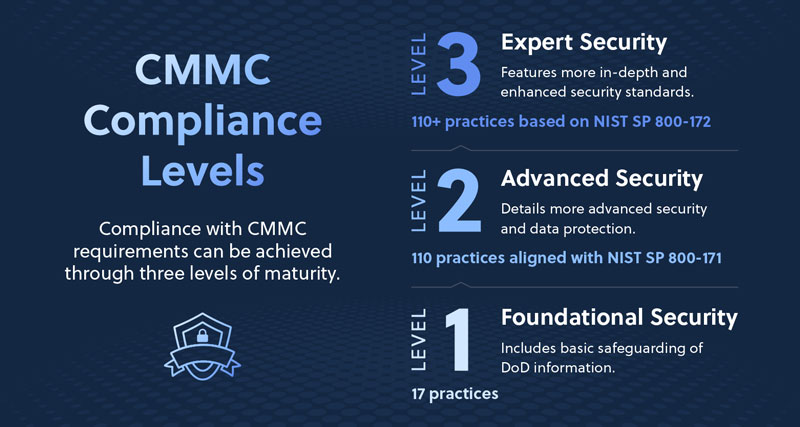
As cybersecurity threats continue to rise and regulatory requirements tighten, organizations supporting government contractors must...

In 2025, cyber threats are in almost every nook and corner. They might be with...

Password managers keep our online accounts safe. They store all our passwords in one place....


Cyber hygiene is super important. It’s like brushing your teeth but for your online life. ...


Passwords unlock our digital lives. We use them for email, bank accounts, and more. Remembering...

The Internet of Things is growing day by day. More devices are connecting to the...

When it happens, you feel powerless. You get an email or letter from a business...
Contact us now to explore customized IT solutions that drive efficiency, security, and success for your business.