Navigating the Recent CrowdStrike IT Outages: How Boston Managed IT Is Here to Support You

FIX: Original Post: Today, the tech world is experiencing significant IT system outages, which are attributed to CrowdStrike. This incident has disrupted various industries, leaving many businesses scrambling to restore their operations. At Boston Managed IT, we want to assure you that we are closely monitoring the situation and are ready to assist you with […]
iPhone Running Slow? Speed It up with One of These Tips

Is Your Business Losing Money Because Employees Can’t Use Tech?

Shiny new tech can be exciting! It promises increased efficiency, happier employees, and a competitive edge. It’s also necessary to stay competitive in today’s technology-driven business world. But that promise can turn into a financial nightmare if you neglect two important things. These are employee training and change management. You can end up losing money […]
10 Easy Steps to Building a Culture of Cyber Awareness

What Were the Coolest Consumer Products Showcased at CES 2024?

Smart Tips for Building a Smart Home on a Budget

Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you even crawl out of bed. A simple voice command adjusts the temperature to your perfect setting. This is no longer just something out of a sci-fi movie. Today’s smart technology seamlessly integrates with your […]
Guide to Improving Your Company’s Data Management

Welcome Thomas Conley: Our New Level 1 Support Engineer for the Summer

We are delighted to announce that Thomas Conley has joined the Boston Managed IT team as a Level 1 Support Engineer for the summer. Thomas comes to us with a strong enthusiasm for technology and a commitment to providing exceptional IT support. About Thomas Thomas is pursuing his degree in Information Technology and has demonstrated […]
Don’t Risk It! Why You Shouldn’t Skip Vulnerability Assessments

Cyber threats are a perpetual reality for business owners. Hackers are constantly innovating. They devise new ways to exploit vulnerabilities in computer systems and networks. For businesses of all sizes, a proactive approach to cybersecurity is essential. One of the most crucial elements of this approach is regular vulnerability assessments. A vulnerability assessment is a […]
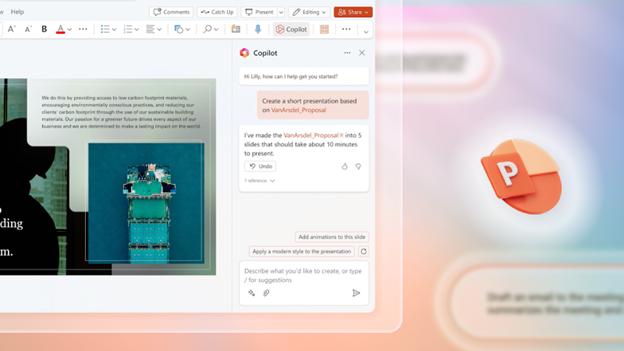
4 Ways Small Businesses Can Leverage Copilot for Microsoft 365